If you'd like to set up PrecisionLender authentication via a Microsoft Azure Active Directory, you will first need to create a new Enterprise Application within your Azure AD.
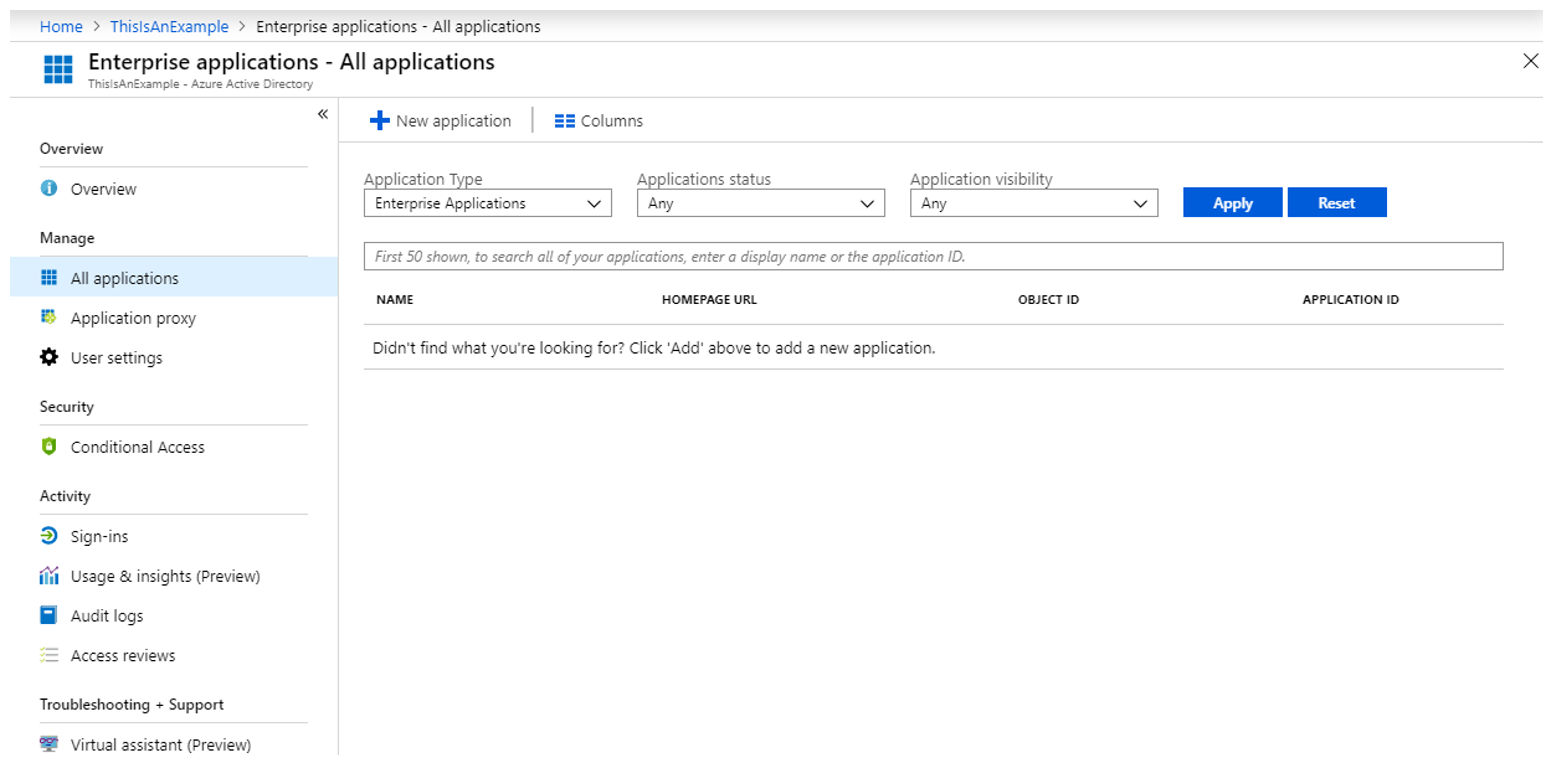
- Log into your Azure Portal ( https://portal.azure.com ), navigate to your Azure Active Directory, and then click on Enterprise Applications.
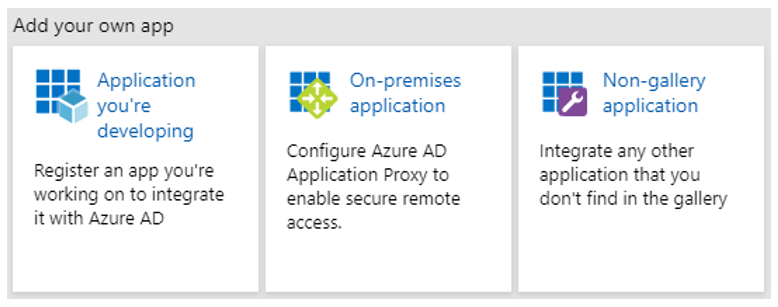
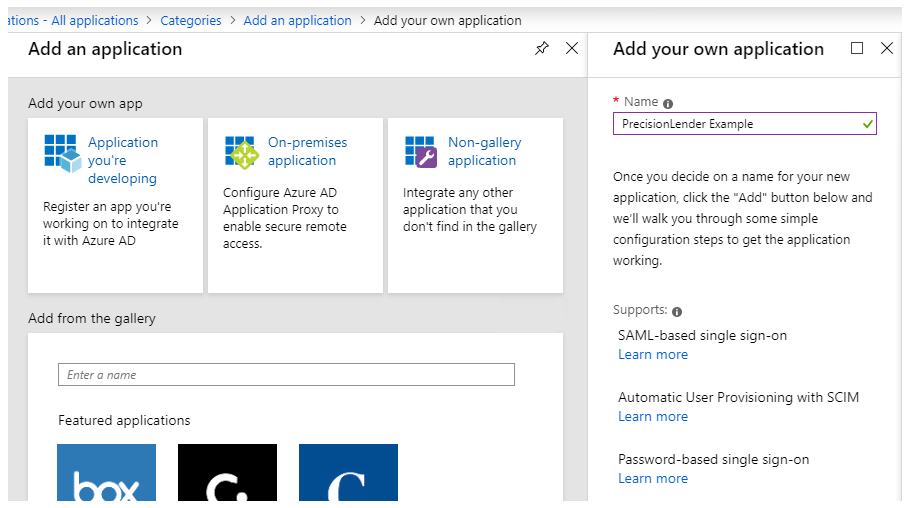
- Click on New application and choose Non-gallery application.
- Enter a name for the application such as PrecisionLender.
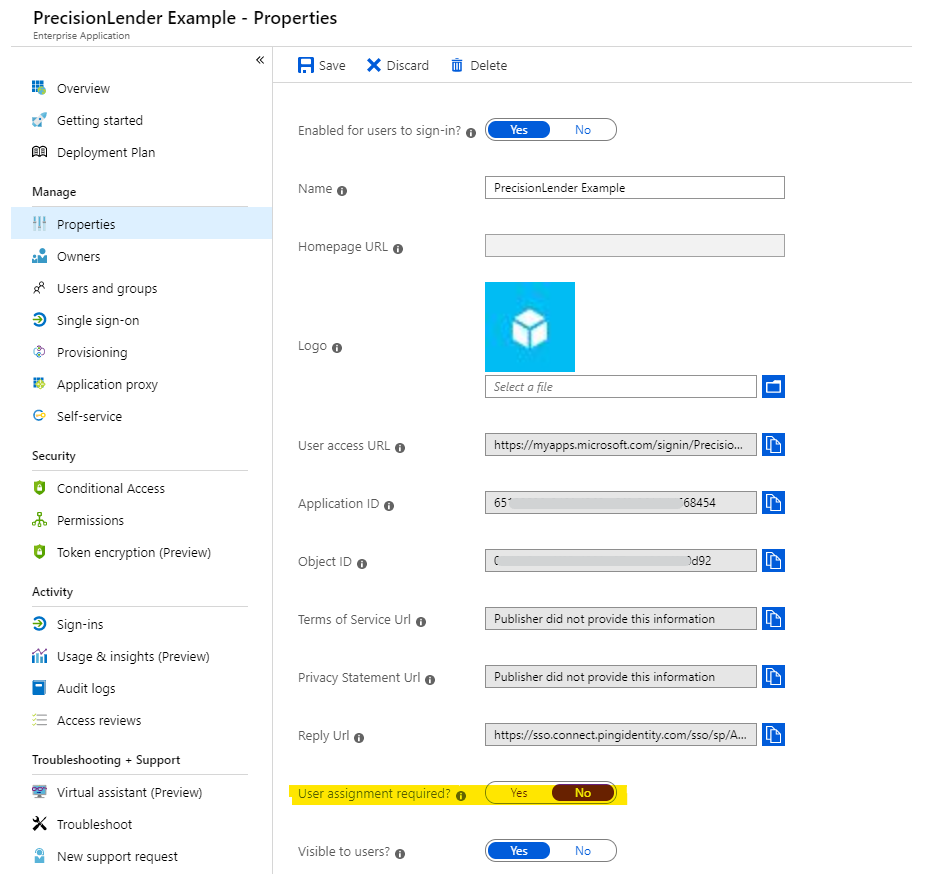
- If you'd like for any AD user to be able to attempt a login regardless of assignment within your AD, go to the Properties tab and change User assignments required to No. Note that users will still need to have an active user account within PrecisionLender to actually log into the system. This option merely allows them to attempt the SSO login process past the point of your AD.
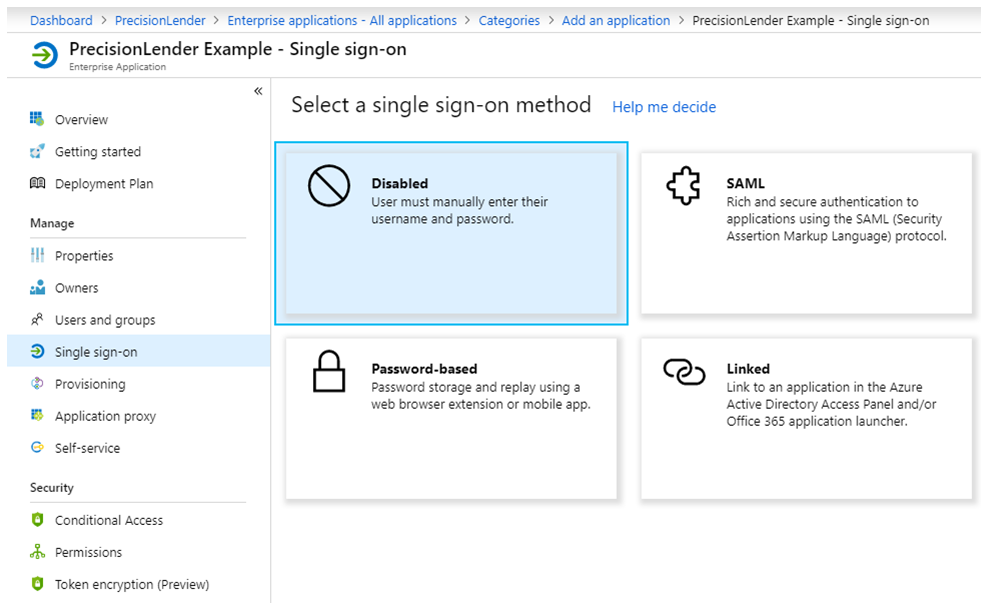
- Go to the Single sign-on tab for your application and choose the SAML option.
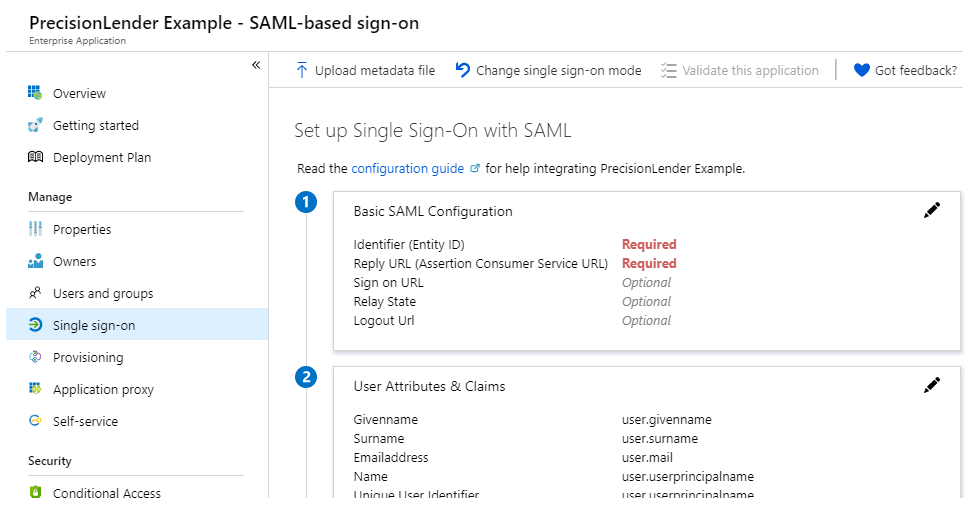
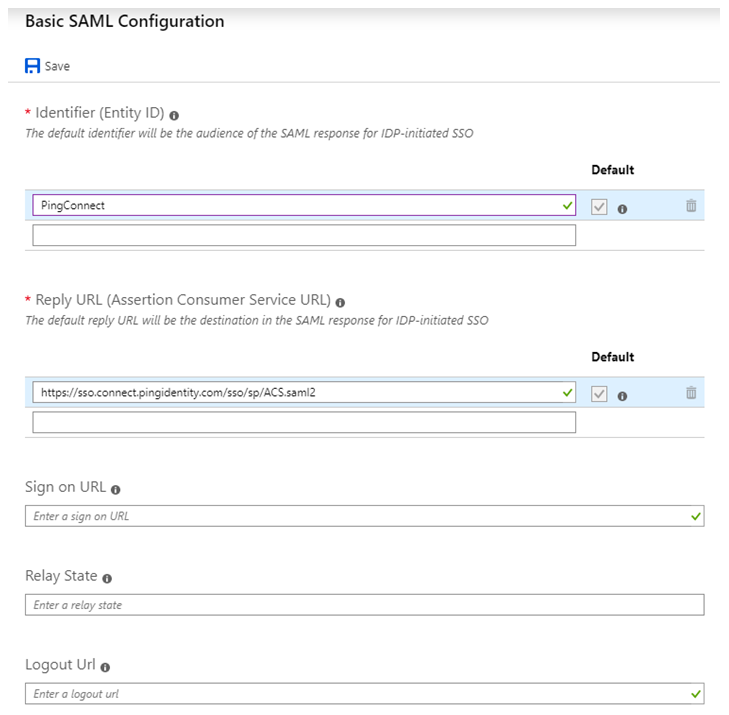
- You will be required to enter the following two values in order to save your configuration
- Identifier (Entity ID): PingConnect
- Reply URL (ACS URL): https://sso.connect.pingidentity.com/sso/sp/ACS.saml2
-
Sign on URL or Relay State URL: This is only required if initiating sign on directly from Azure. If you will be using this method for initiating sign in, please let us know and we will provide the specific URL to enter. If you will be using a completely IDP initiated workflow, please connect with our Support team.
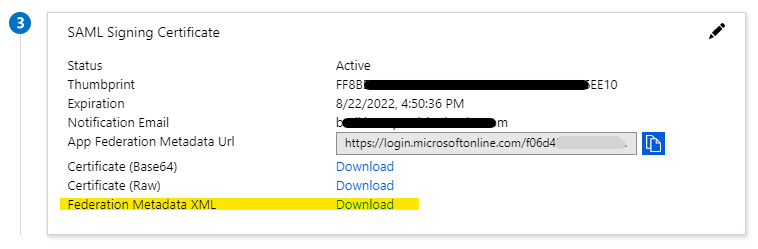
- On the Single sign-on tab, Download the Federation Metadata XML file to your local computer. You will then need to provide this file to the PrecisionLender support team in order for us to complete your SAML setup.